Warning! When Big Data Turns Bad
Big data is proving its usefulness in fields as diverse as improving healthcare and cutting crime. However, as with all…
What Every Business Owner Needs to Know About Data Sovereignty
Sovereignty isn’t usually the first word that comes to mind when thinking about data. With all the recent data fiascos,…
Meeting the Business Technology Needs of Midsized Companies
Current technology trends are important for all organizations. Most midsized companies have these technologies at the top of their lists:…
The Complex Process of Keeping Access Governance Software Simple
With the rapid growth of the access governance software market, you would think that access certification issues would be a thing of…
The Harmful Side of Big Data: Identity Theft
According to a recent report published by the Identity Theft Resource Center, more than 368 big data breaches have been…
How Virtualization Can Improve Security
Virtualization can do a lot for a company. It can increase a business’s efficiency, doing more work with less equipment.…
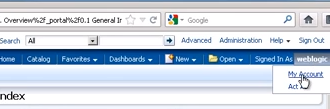
How to Create Users in Oracle BI (OBIEE) and WebLogic Tutorial
This short guide will take you through the process of creating new users in Oracle OBIEE and WebLogic as well…
How to Keep Your iCloud Account Safe From Hackers
Since hackers leaked nude photos of more than 100 celebrities from their phones to the Internet, people have been concerned…
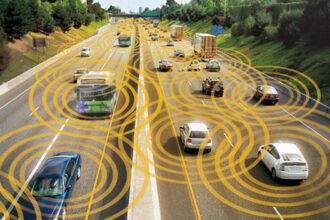
The Societal Shift of Self Driving Cars
We are currently approaching a cross roads in transportation that we really haven’t seen since the transition from the horse…
Who Is Paying the Bill for Data Breaches? [INFOGRAPHIC]
Data breaches have become a common thing of today unfortunately. Many companies that store massive amounts of credit cards, passwords…