Facebook’s ThreatExchange to Help Cyber Security Experts Coordinate Their Efforts Against Hackers
Hackers continue to target companies throughout the United States with cyber attacks. In 2014, cyber attacks hit a rapid pace…
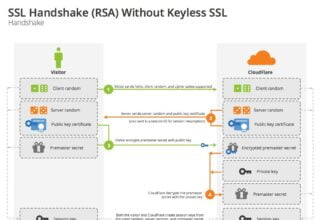
A Look at How Keyless SSL Works
Secure Socket Layer, or SSL for short, is one of the key elements to providing a safe and secure web…
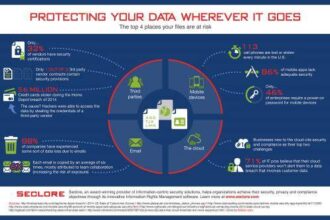
Protecting Your Data Wherever It Goes [INFOGRAPHIC]
Many of today’s businesses have moved on from the large metal filing cabinets of yore, replacing them with digital files,…
From Police to Partner: The Changing Role of IT
When evaluating business applications, the average non-technical employee probably knows as much about security and compliance as he does about…
Scary Security Concerns With the Internet of Things
With new technology comes concerns about security. When it comes to the relatively new Internet of Things (IoT), there are…
Dynamic Cybersecurity Needs: Reassessing Security
As a recent report on Defending Data by Nuix found, cybersecurity needs are dynamic - 73 percent of surveyed participants…
Big Data Ethics and Your Privacy [INFOGRAPHIC]
Big data enables to check, control and know everything. But to know everything entails an obligation to act on behalf…
Mobile Apps, Business Apps and Network Security
Ours is a world of gadgets. There was a time when the refrigerator was revolutionary. Now we label our devices…
Protecting Your Business from Shellshock
By now, most of you have heard of the digital threat facing network security called Shellshock. For those who haven’t,…
Self-Healing Virtual Machines Coming to Datacenter Near You?
One of the more exciting inventions in data center technology has been developed by a team of computer scientists from…