A Quick Tech Tutorial: Two-Factor Authentication
Two-factor authentication is a best practice to fulfill authorization and authentication requirements for HIPAA compliance or PCI DSS compliance and…
Turn Analysis Into Action: 3 Tips
Today’s analytics tools offer deeper insights into your data than ever before. But if you were to take an objective…
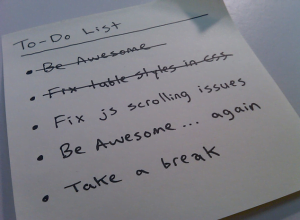
Software Development Project: Dot Your “I”s and Cross Your “T”s
A checklist for maintaining control over software development projectsHow can you ensure control over your software development project? Selecting a…
Headaches, Data Analysis, and Negativity Bias
I have suffered from bad headaches most of my life, but over the last few years they seemed to be getting…
Choosing Your Business Intelligence Solution: Don’t Be Afraid of the “Smoosh-ins®”
When an enterprise selects a BI solution, it should be able to get the combinations of BI functionality that best…
Mobile Technology in Data Centers: After the Cloud, What Next?
What does the future hold for the data center industry? Yan Ness, Co-CEO of Online Tech, gives his thoughts on…
How Real Revenue Is Derived from Big Data [INFOGRAPHIC]
Jeff Kelly, a principal research contributor of Wikibon, provides his commentary on the reality of big data and its application and…
Design a Successful Business Dashboard: 3 Essential Tips
So you are all set to design a swanky new dashboard that would be your next masterpiece? Have you already…
Shortage in Advanced Analytic Skills? Here’s an Indirect Approach
There are lots of articles these days about the challenges of recruiting enough data scientists, predictive analytic specialists or data…
Societal Remedies for Algorithms Behaving Badly
In a world where computer programs are responsible for wild market swings, advertising fraud and more, it is incumbent upon…