The Defense Industrial Base (DIB) is always under constant ransomware attacks. The malicious actors behind these attacks often block access to sensitive government data, intellectual property, and even trade secrets until they get paid. This can potentially harm a government’s military capabilities and operations.
According to the Symantec Internet Security Threat Report of 2016, governments’ growing dependence on information technology makes them vulnerable to ransomware attacks. Hackers perpetrate ransomware attacks against the defense industrial base to undercut the military, technological, and economic advantages of a government.
How to Secure the DIB Against Ransomware Attacks
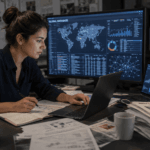
In recent years, cyber threats have been continuously evolving. DIB networks host critical operational assets and data that is crucial to national security. If the systems get breached, national security will be compromised. Hackers have been enhancing their attack methods, thus the need for governments to have a robust cybersecurity posture to secure the DIB. Here’s how to secure the defense industrial base against ransomware attacks:
Proactive Defense of DIB Networks
Ideally, organizations should impede threats before they reach the intended targets. However, this is not often the case because most threats reach their targets before getting detected. Governments should be proactive in securing their DIB networks. This entails undertaking a real-time situational analysis of DIB networks and the entire supply chain.
In unprecedented times such as the current COVID-19 pandemic, this can be difficult. Organizations are faced with the challenge of meeting their obligations to the DIB. They must also protect their employees through measures such as social distancing. To prevent ransomware attacks during the pandemic, the federal government classified the DIB as a critical infrastructural sector. This proactive approach has prevented potential ransomware attacks on vital installations.
Implement an All-Inclusive Cybersecurity Stance
Human actors are the weakest link when it comes to cybersecurity. Individuals who work in a DIB supply chain handle sensitive and proprietary data that is attractive to hackers. Often hackers steal the credentials of these individuals to access DIB networks. Obtaining a password is enough to access and compromise a critical system.
Those who work in DIB supply chains should be the first and last line of defense in preventing ransomware attacks. Your cybersecurity strategy should start and end with people who work in the DIB supply chain. These individuals are responsible for ensuring that the network is secure. Therefore, you should work with them to prevent ransomware attacks.
Regular Behavioral Analysis
Many ransomware attacks targeting DIB networks can be prevented by implementing a mechanism for monitoring users’ behavioral patterns. This includes detecting even the slightest changes in human habits. The widely-publicized Sea Dragon Attack could have been prevented if the US government had a mechanism for detecting unusual access to its DIB networks.
Regular behavioral analyses help you to have a better understanding of the DIB supply chain. It provides an added layer of defense that makes the supply chain less susceptible to ransomware attacks. In this regard, consider setting up a system for monitoring potential risk based on users’ behavior. You should measure this against an established standard. Deviations from the normal behavioral patterns can trigger signals that anomalies have been detected.
Engage in Security-by-Design
Most ransomware attacks catch you by surprise. To avoid these unpleasant surprises, you should engage in “security-by-design” rather than “security-as-an-afterthought.” By prioritizing cybersecurity when designing your DIB supply chain, it will be easier to prevent ransomware attacks. Likewise, you’ll be more susceptible to ransomware attacks if you only start prioritizing security after facing a breach.
Adhere to Government-Issued Guidelines
Due to the growing number of ransomware attacks, the American government dedicated resources and time to secure its defense industrial base. If your organization is part of the DIB supply chain, it’s best to keep in mind that it can be an attack vector. Therefore, it’s in your best interest to act upon all the recommendations provided by the government.
Recently, the Cyberspace Solarium Commission issued a report highlighting the government’s preparedness for cyberattacks. According to the report, the government doesn’t have the full capacity to act with the agility and speed required to defend its cyberspace.
To bridge the cybersecurity gap and ensure that the DIB is protected fully, organizations should follow all government-issued regulations. This includes sharing threat data with the department of defense and proactively hunting for threats within their networks. In doing so, you’ll be playing a significant role in securing the DIB.
Final Words
The adversary penetration of defense industrial base systems and networks poses an existential threat to national security. The abundance of ransomware attacks targeting DIB networks makes it necessary for government agencies and private organizations to work together and stop these attacks. This is the only way of ensuring that the cybersecurity stance of a country remains strong. Consequently, all malicious ransomware attacks against DIB networks and systems will be thwarted.