Working With Your IT Department to Improve Corporate Efficiency
For a while now, companies have been re-evaluating their commitment to onsite IT because there are other options available that…
Securing Your Data by Protecting It Against Spam
Interestingly, most site owners out there do not actually think about security. That is a really bad thing because of…
The USA Is Building the World’s Fastest Supercomputer
The United States president, Barack Obama, wants a new supercomputer for the United States and signed an executive order for…
Best Practice Cloud Security: Is Your Cloud Secure Inside and Out?
Learn to use the Cloud security principles to reassure your customers. Last year, the UK government’s Cabinet Office outlined what…
eCommerce Security: How to Control User Access to Your Environment
eCommerce security risks are ever increasing; the costs of breach is more than just about lost sales, so find out…
Migrate from Proprietary Software to Linux to Create Cost Savings
Amongst the top IT trends of the moment is the development of Linux Containers. Financial and technical investors, Linuxsoftware programmers and…
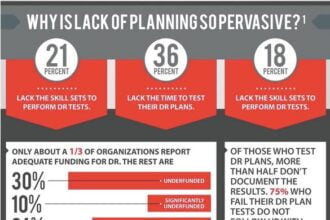
6 Steps to Data Disaster Recovery [INFOGRAPHIC]
More than 70 percent of companies are not currently confident in their ability to restore data in the case of…
Big Data Security: Why It’s a Problem and What We Can Do About It
This is unequivocally the era of big data — but it is not necessarily the era of big data security.…
Rent-A-Botnet Free Cloud-Based Servers May Encourage Cyber Warfare
As the Internet has become an integral part of our economic and personal lives, hackers have found new ways to…
As the Internet of Things Mobilizes, Safeguarding the Cloud Is Our Prerogative
Test case: the connected carThe idea of the connected car is a reality. Connected car technology precedes cars from Google and Apple…